Use cases
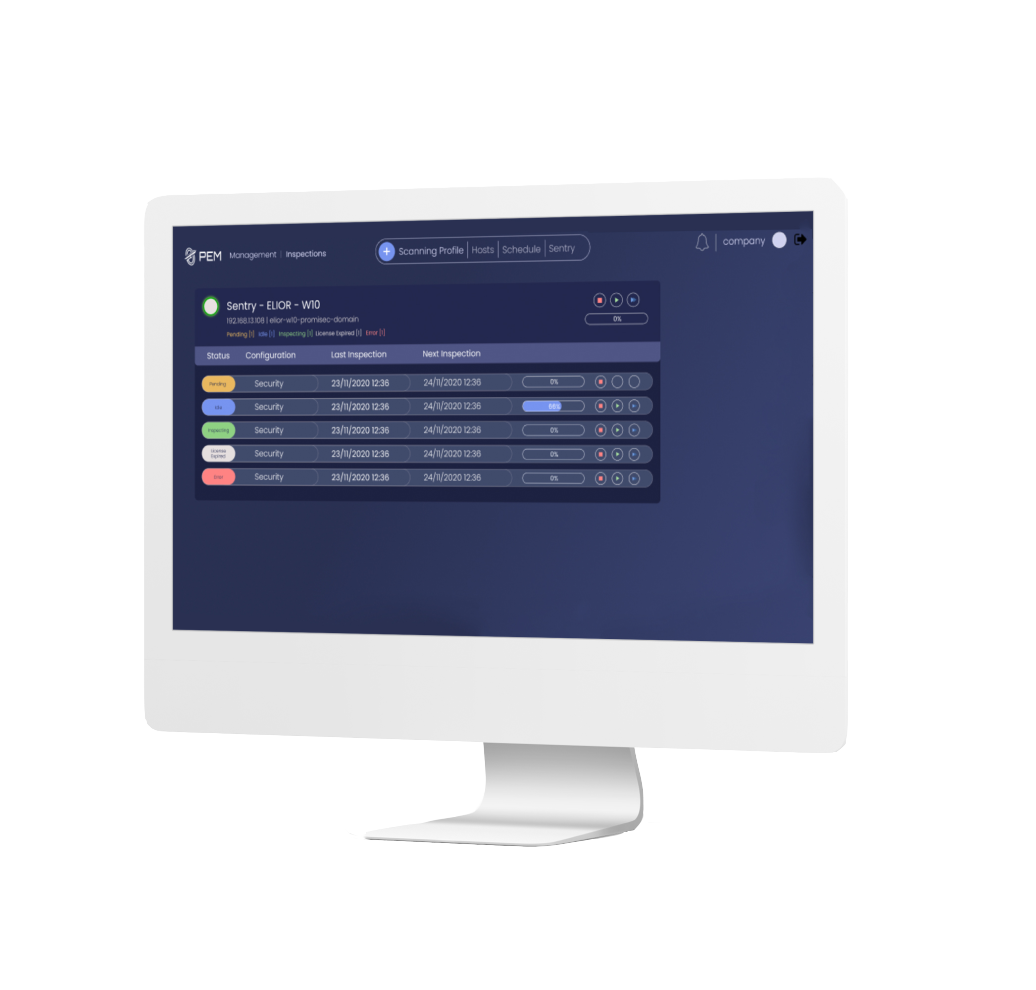
Promisec Endpoint Manager contains within it a multitude of tools, and has applicable capabilities for employees at every level of the organization.
Whether for the strategic and administrative challenges of the CISO, the monitoring challenges of the SOC team, or the security challenges of the system management, PEM has a solution.
The various use cases which PEM is capable of include full organizational visibility, automated reporting, and analysis capabilities which can be used to identify and deal with security issues at the lowest levels.