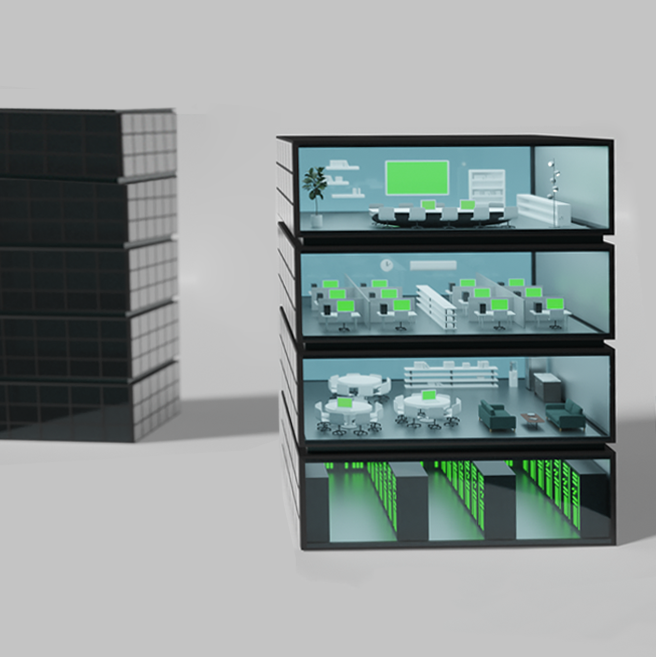
Holistic endpoint
security
Compliance, Management & Threat Detection
Inspect
Pioneering and unique in its capabilities, Promisec Endpoint Manager provides deep, accurate, and near- instant visibility and remediation throughout your entire network.
Analyze
Promisec Endpoint Manager, or PEM, is built around the idea that real endpoint security begins with visibility – you can’t fix what you can’t see.
Remediate
PEM inspects every endpoint in your organization, identifies security gaps, and reports back to you in seconds.
Report
This inspection is agentless, which means it doesn’t affect the performance of your endpoints, and the results are presented in an intuitive and comprehensive dashboard.